这篇文章主要介绍了如何使用Python多线程测试并发漏洞,文中通过示例代码介绍的非常详细,对大家的学习或者工作具有一定的参考学习价值,需要的朋友可以参考下
需求介绍
有时候想看看Web应用在代码或者数据库层有没有加锁,比如在一些支付、兑换类的场景,通过多线程并发访问的测试方式可以得到一个结论。
步骤
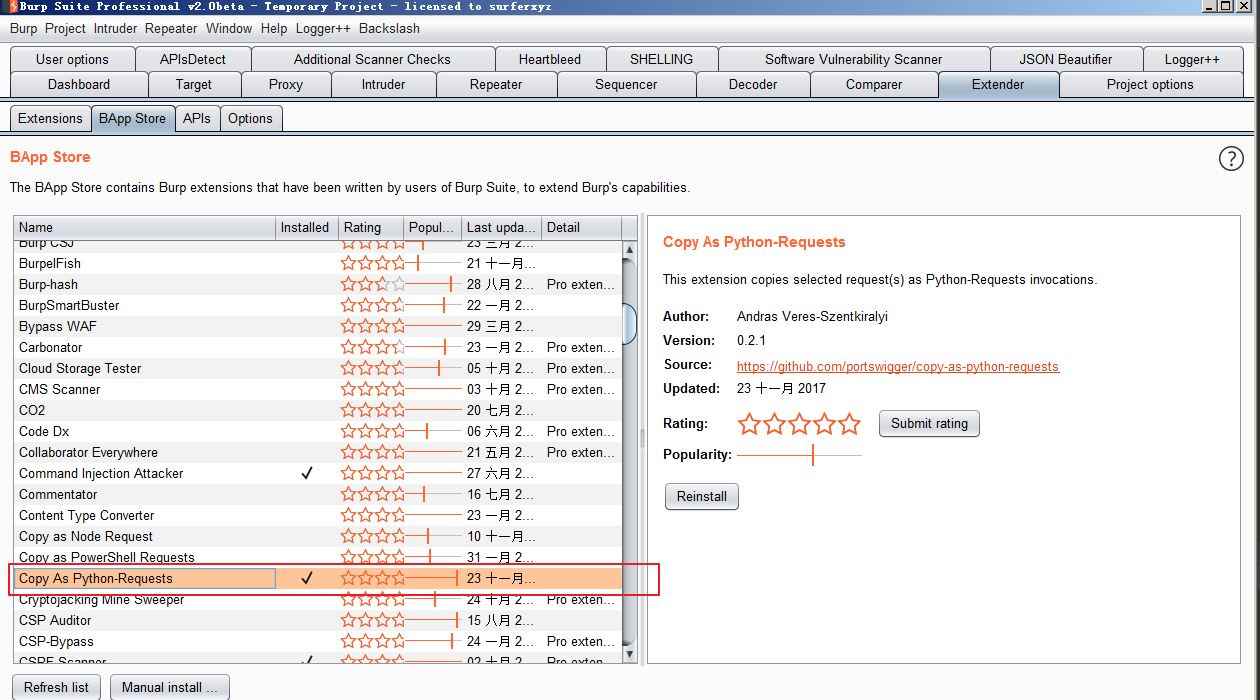
1. Burp Suite安装插件
安装一个Copy As Python-Requests插件,提高编码效率;
2. 拦截包并拷贝发包的代码
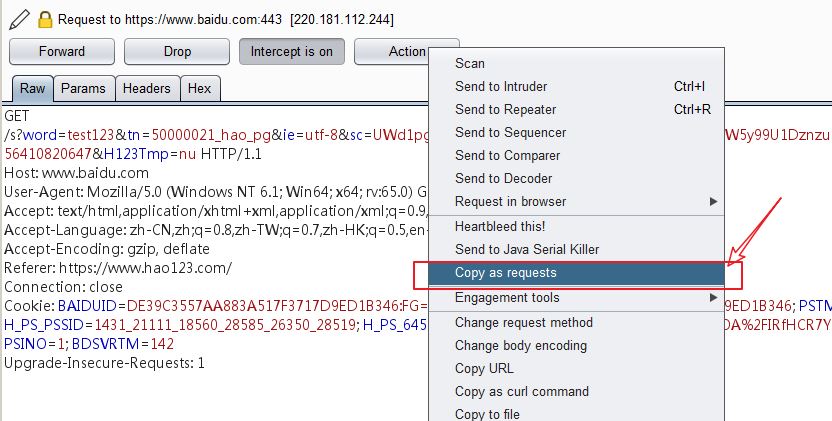
打开一个文本编辑器,右键粘贴出来:
import requests
burp0_url = "https://www.baidu.com:443/s?word=test123&tn=50000021_hao_pg&ie=utf-8&sc=UWd1pgw-pA7EnHc1FMfqnHRdnHfkP163PWD3PzuW5y99U1Dznzu9m1Y1rj0zPjRYP1Ds&ssl_sample=s_108&srcqid=2890185856410820647&H123Tmp=nu"
burp0_cookies = {"BAIDUID": "DE39C3557AA883A517F3717D9ED1B346:FG=1", "BIDUPSID": "DE39C3557AA883A517F3717D9ED1B346", "PSTM": "1548660573", "BD_UPN": "13314352", "H_PS_PSSID": "1431_21111_18560_28585_26350_28519", "H_PS_645EC": "0701XLkxqPa8GpBa6wBJs%2BrZyNuhMOA%2FIRfHCR7YuUcETmxXSKm0g32CT0c", "delPer": "0", "BD_CK_SAM": "1", "PSINO": "1", "BDSVRTM": "142"}
burp0_headers = {"User-Agent": "Mozilla/5.0 (Windows NT 6.1; Win64; x64; rv:65.0) Gecko/20100101 Firefox/65.0", "Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8", "Accept-Language": "zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2", "Accept-Encoding": "gzip, deflate", "Referer": "https://www.hao123.com/", "Connection": "close", "Upgrade-Insecure-Requests": "1"}
requests.get(burp0_url, headers=burp0_headers, cookies=burp0_cookies)3. 运行Python多线程代码
将生成的python代码粘贴到action( )函数里面即可;
import threading
import requests
threads = []
def action():
burp0_url = "https://www.baidu.com:443/s?word=test123&tn=50000021_hao_pg&ie=utf-8&sc=UWd1pgw-pA7EnHc1FMfqnHRdnHfkP163PWD3PzuW5y99U1Dznzu9m1Y1rj0zPjRYP1Ds&ssl_sample=s_108&srcqid=2890185856410820647&H123Tmp=nu"
burp0_cookies = {"BAIDUID": "DE39C3557AA883A517F3717D9ED1B346:FG=1", "BIDUPSID": "DE39C3557AA883A517F3717D9ED1B346",
"PSTM": "1548660573", "BD_UPN": "13314352", "H_PS_PSSID": "1431_21111_18560_28585_26350_28519",
"H_PS_645EC": "0701XLkxqPa8GpBa6wBJs%2BrZyNuhMOA%2FIRfHCR7YuUcETmxXSKm0g32CT0c", "delPer": "0",
"BD_CK_SAM": "1", "PSINO": "1", "BDSVRTM": "142"}
burp0_headers = {"User-Agent": "Mozilla/5.0 (Windows NT 6.1; Win64; x64; rv:65.0) Gecko/20100101 Firefox/65.0",
"Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8",
"Accept-Language": "zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2",
"Accept-Encoding": "gzip, deflate", "Referer": "https://www.hao123.com/", "Connection": "close",
"Upgrade-Insecure-Requests": "1"}
requests.get(burp0_url, headers=burp0_headers, cookies=burp0_cookies)
if __name__ == '__main__':
print("Threading ready:")
for i in range(0,100):
t = threading.Thread(target=action)
t.setDaemon(True) // 开启守护进程,如果宿主进程挂了,不用执行完全部线程任务也要立即结束。 参考 https://www.cnblogs.com/Haojq/p/10278365.html
t.start()
print("Threading ran end!")4. 确认结果
查看领取的结果是否有超过原本的数量,如果超过就原本可领的数量,那就666了。
以上就是本文的全部内容,希望对大家的学习有所帮助,也希望大家多多支持脚本之家。